Expert Security Advice When You Need It Most.
Project-based cybersecurity advisory for organizations navigating complex decisions — security program reviews, M&A cyber risk, board briefings, and independent second opinions.
Advisory & Consulting
Specialist guidance on the security decisions that matter most.
Security Program Reviews
An independent audit of your security posture — policies, controls, and technical hygiene — with a prioritized improvement roadmap.
Delivered in 2–4 weeks, board-ready output.
Board & Investor Briefings
Executive-level presentations that translate cyber risk into business impact — liability, revenue exposure, and remediation cost.
Credible, jargon-free, decision-ready.
M&A Cyber Due Diligence
Pre-close cyber risk assessment to identify hidden liabilities, compliance gaps, and post-acquisition remediation costs.
Used by PE firms and corporate acquirers.
Why Choose Our Service
Experience the difference with our comprehensive approach.
Expert-Led Approach
Our team consists of certified cybersecurity professionals with years of hands-on experience.
Comprehensive Coverage
We provide end-to-end security testing across all your digital infrastructure.
Actionable Results
Get clear, prioritized recommendations that your team can implement immediately.
Ongoing Support
We don't just test and leave - we provide continuous guidance and support.
Insight
Stay ahead with the latest publications, research briefs, and expert perspectives on cybersecurity.
Web App Penetration Testing
Driving Portfolio-wide Value with Cybersecurity
Atumcell Publications
Explore our latest whitepapers, case studies, and reports designed to strengthen security strategy.
Frequently Asked Questions
CISO as a Service is an ongoing retainer providing executive-level security leadership month to month. Advisory & Consulting is project-based — you bring us in for a defined scope and duration: a security program review, an independent assessment ahead of a board presentation, or a second opinion on a vendor proposal. No retainer required.
We evaluate your current security posture across people, process, and technology: policies, controls, third-party risk, incident response readiness, and technical hygiene. We identify gaps relative to your target maturity and produce a prioritized roadmap with effort, cost, and risk-reduction estimates. Typical duration is 2–4 weeks.
Yes. We regularly present to boards, audit committees, and investor groups. We translate technical findings into business risk language — revenue impact, liability exposure, regulatory consequence — and provide recommendations the board can act on.
Yes. We work alongside legal and financial diligence teams to assess target company cyber posture before close. We identify hidden liabilities (prior breaches, weak controls, compliance gaps) and quantify remediation costs so the deal team can adjust valuation or negotiate representations and warranties insurance.
Our advisory work spans private equity, manufacturing, energy, healthcare, financial services, and B2B software. We adapt our recommendations to the regulatory environment, threat landscape, and operational constraints specific to your sector.
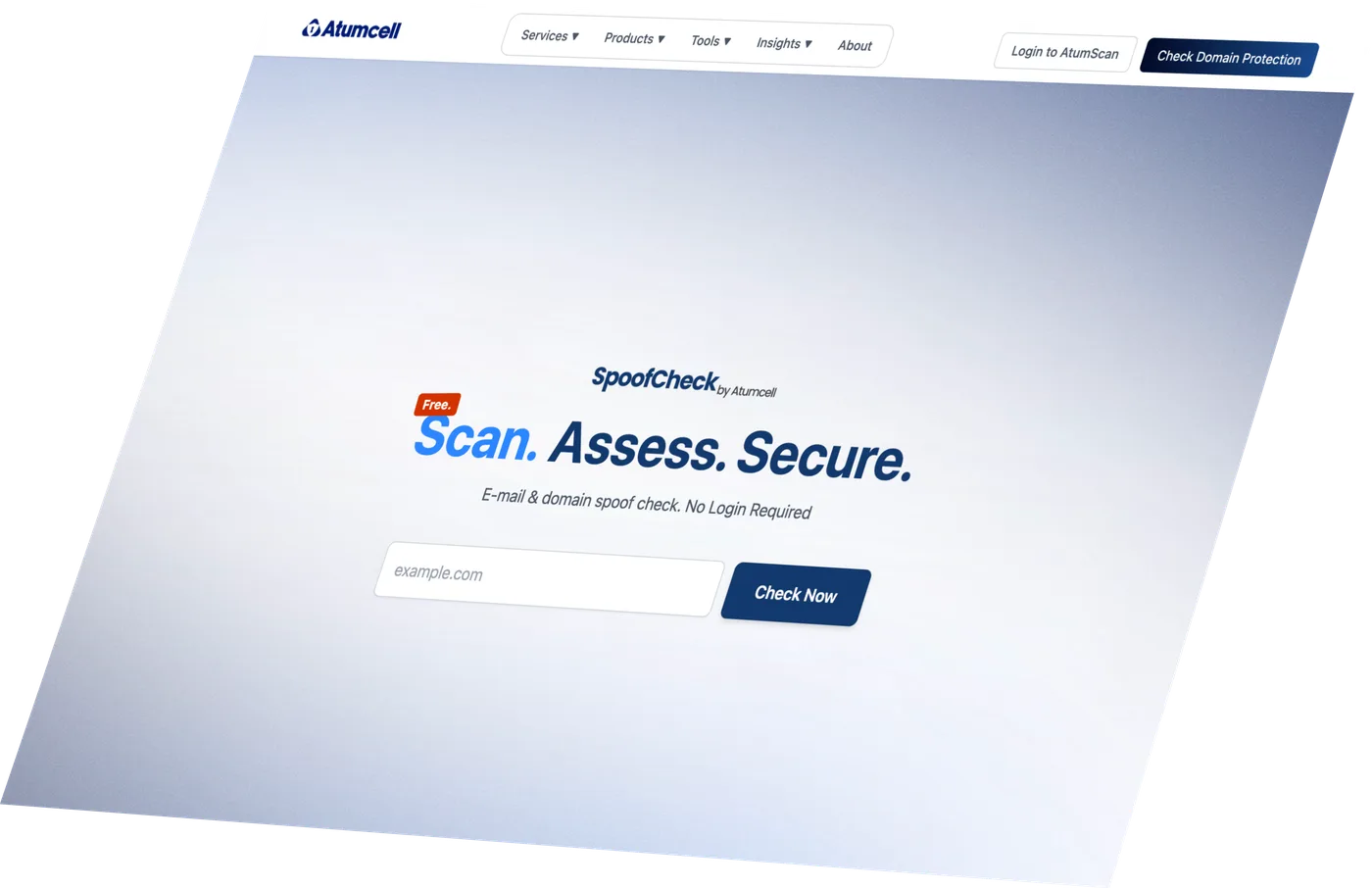
Discover Your
Cyber Risk Level.
Find out in seconds if your domain can be spoofed. Free, no login required.
Fixed-scope pricing agreed before we start · Actionable insights · No commitment required