Cloud Security Services
Secure your cloud infrastructure with specialized security assessments and compliance frameworks.
Cloud Security Solutions
Specialized security services for cloud infrastructure and platforms.
AWS Security Assessment
Comprehensive security evaluation of your AWS infrastructure and configurations.
We ensure your AWS environment follows security best practices.
Azure Security Testing
Specialized testing for Microsoft Azure cloud environments and services.
Secure your Azure infrastructure with our proven methodologies.
Multi-Cloud Security
Cross-platform security assessment for hybrid and multi-cloud environments.
Comprehensive security across all your cloud platforms.
Why Choose Our Service
Experience the difference with our comprehensive approach.
Expert-Led Approach
Our team consists of certified cybersecurity professionals with years of hands-on experience.
Comprehensive Coverage
We provide end-to-end security testing across all your digital infrastructure.
Actionable Results
Get clear, prioritized recommendations that your team can implement immediately.
Ongoing Support
We don't just test and leave - we provide continuous guidance and support.
Insight
Stay ahead with the latest publications, research briefs, and expert perspectives on cybersecurity.
Web App Penetration Testing
Driving Portfolio-wide Value with Cybersecurity
Atumcell Publications
Explore our latest whitepapers, case studies, and reports designed to strengthen security strategy.
Frequently Asked Questions
We cover AWS, Microsoft Azure, and Google Cloud Platform, as well as hybrid environments. We have expertise with Kubernetes, containerized workloads, serverless functions, and infrastructure-as-code (Terraform, CloudFormation).
A cloud security assessment reviews configuration, IAM, permissions, and architecture to identify risks that a penetration test or vulnerability scan may miss. A penetration test focuses on actively testing running applications, containers, workloads, and exposed perimeter services within the cloud environment. We usually recommend starting with the assessment first for full visibility and better testing priorities.
Yes. Identity and access management is one of the most common sources of cloud breaches. We review IAM roles, policies, cross-account trust relationships, and privilege escalation paths as a core part of every cloud engagement.
Yes. Container and Kubernetes security is a core part of our cloud offering. We review cluster RBAC, pod security policies, network policies, image security, secrets management, and runtime configurations. We test for common container escape techniques and lateral movement paths within orchestrated environments.
Our cloud assessments map findings to CIS Benchmarks (AWS, Azure, GCP), SOC 2 Trust Service Criteria, ISO 27001 Annex A controls, and NIST SP 800-53. For regulated industries we also cover PCI DSS cloud scoping requirements and HIPAA technical safeguards.
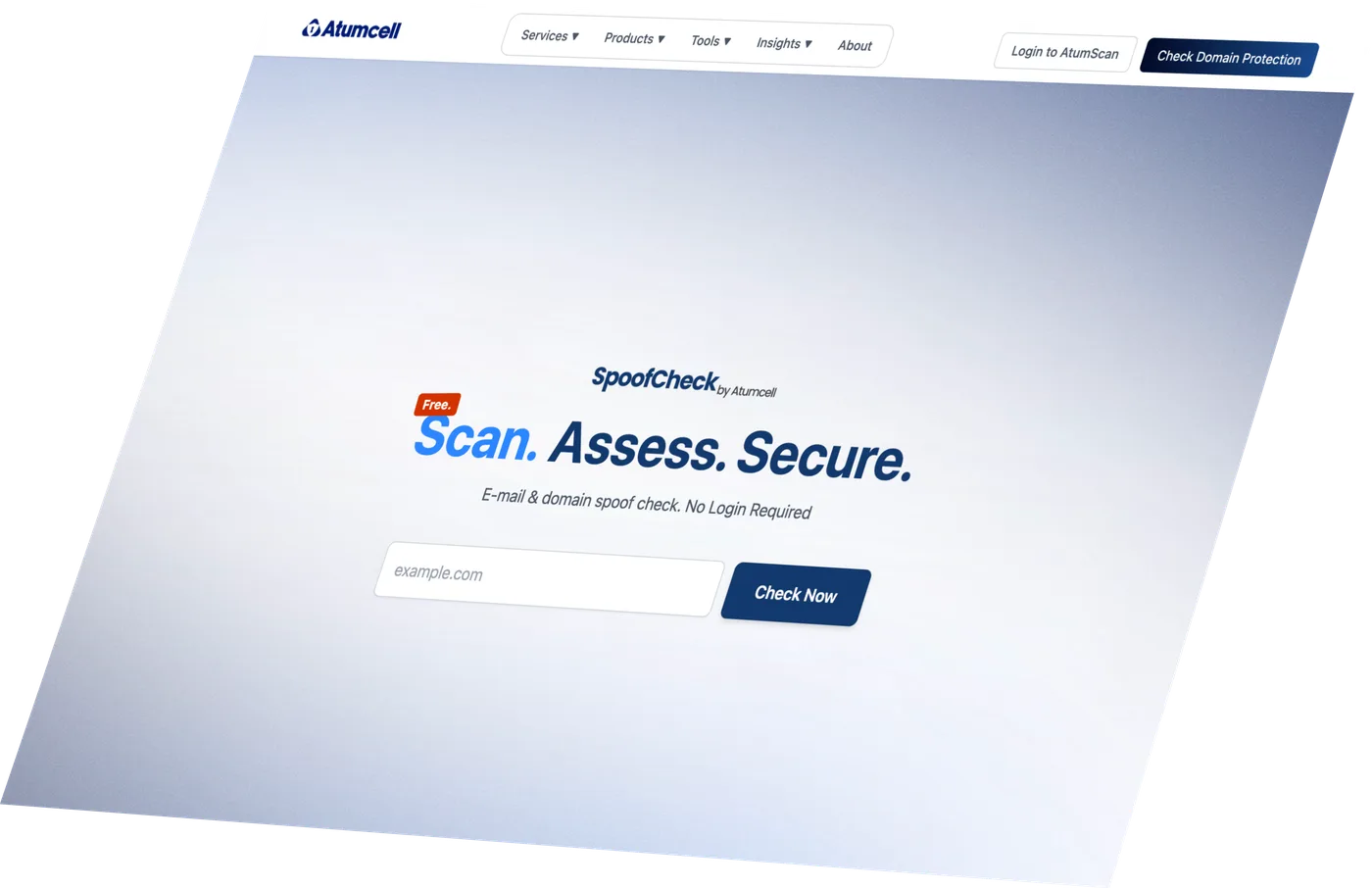
Discover Your
Cyber Risk Level.
Find out in seconds if your domain can be spoofed. Free, no login required.
Fixed-scope pricing agreed before we start · Actionable insights · No commitment required