Penetration Testing Services
Simulate real-world attacks to identify vulnerabilities before malicious actors do.
Penetration Testing Solutions
Comprehensive security testing to identify and fix vulnerabilities.
Network Penetration Testing
Comprehensive testing of your network infrastructure and perimeter defenses.
We test your network security from an attacker's perspective.
Application Security Testing
Deep-dive testing of web applications, APIs, and mobile apps.
Find vulnerabilities in your applications before hackers do.
Social Engineering
Test your human firewall with targeted social engineering assessments.
Evaluate your organization's resistance to social engineering attacks.
Why Choose Our Service
Experience the difference with our comprehensive approach.
Expert-Led Approach
Our team consists of certified cybersecurity professionals with years of hands-on experience.
Comprehensive Coverage
We provide end-to-end security testing across all your digital infrastructure.
Actionable Results
Get clear, prioritized recommendations that your team can implement immediately.
Ongoing Support
We don't just test and leave - we provide continuous guidance and support.
Insight
Stay ahead with the latest publications, research briefs, and expert perspectives on cybersecurity.
Web App Penetration Testing
Driving Portfolio-wide Value with Cybersecurity
Atumcell Publications
Explore our latest whitepapers, case studies, and reports designed to strengthen security strategy.
Frequently Asked Questions
Penetration testing is a controlled security assessment where skilled professionals simulate real-world attacker techniques to identify exploitable vulnerabilities in your systems, applications, and networks — before malicious actors find them.
Vulnerability scanners are automated tools that identify known weaknesses. Penetration testing adds human intelligence: we chain vulnerabilities, attempt real exploits, bypass controls, and demonstrate the actual business impact of each finding. This is context a scanner cannot provide.
Most organizations conduct annual pentests at minimum, with additional testing after significant changes such as new products, cloud migrations, or acquisitions. High-compliance environments often run quarterly or continuous testing programs.
We start with a scoping call to understand your environment, define what's in scope, and agree on rules of engagement. We offer both black-box (no prior knowledge) and grey-box (partial knowledge) engagement models.
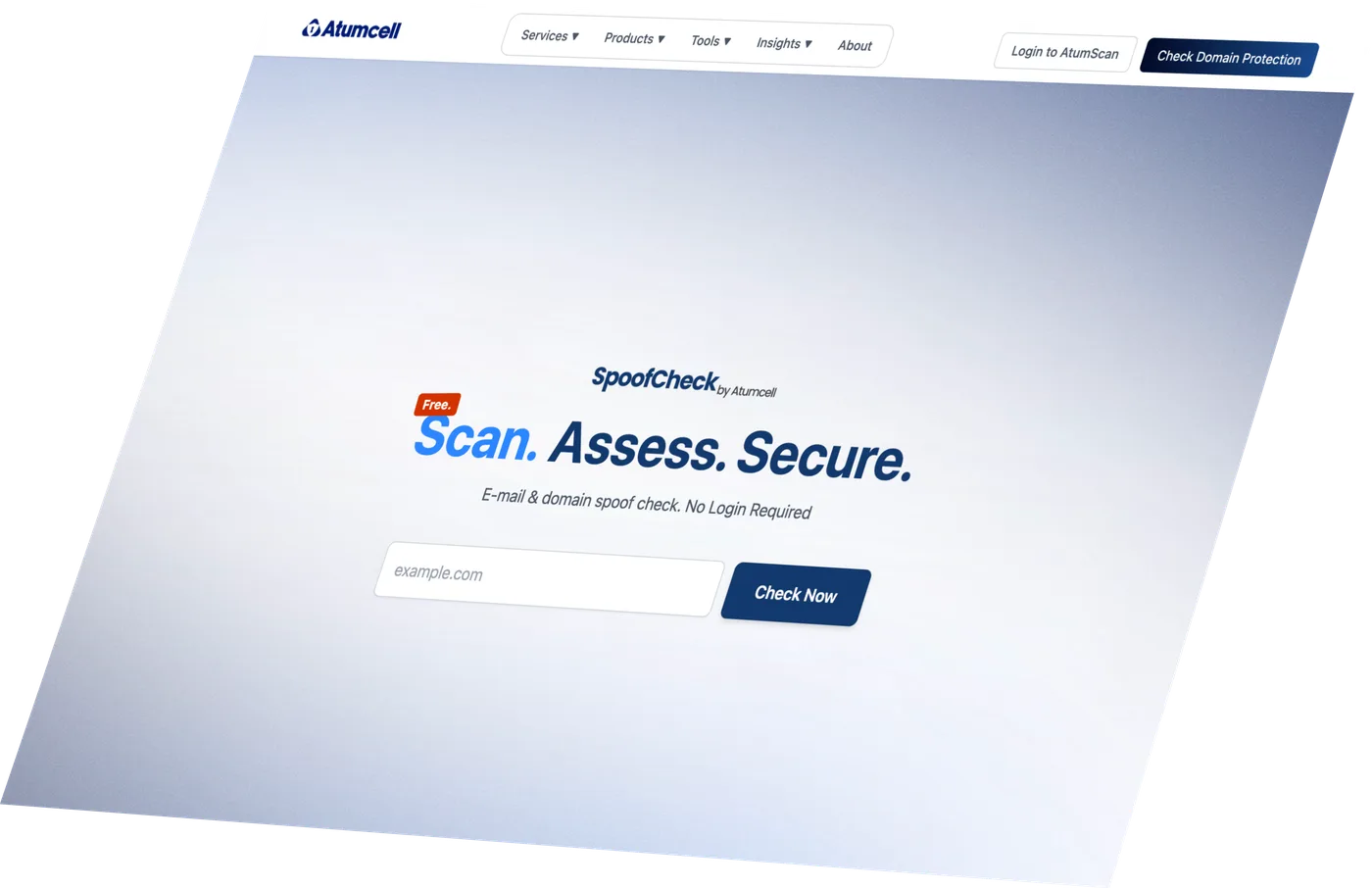
Discover Your
Cyber Risk Level.
Find out in seconds if your domain can be spoofed. Free, no login required.
Fixed-scope pricing agreed before we start · Actionable insights · No commitment required