Web Application Penetration Testing
Secure your web applications with comprehensive security testing and vulnerability assessment.
Web Application Security
Specialized testing for web applications and APIs.
OWASP Top 10 Testing
Comprehensive testing against the OWASP Top 10 web application security risks.
We test for all critical web application vulnerabilities.
API Security Testing
Secure your REST and GraphQL APIs with specialized testing methodologies.
Protect your API endpoints from common attack vectors.
Authentication Testing
Test login mechanisms, session management, and access controls.
Ensure your authentication systems are bulletproof.
Why Choose Our Service
Experience the difference with our comprehensive approach.
Expert-Led Approach
Our team consists of certified cybersecurity professionals with years of hands-on experience.
Comprehensive Coverage
We provide end-to-end security testing across all your digital infrastructure.
Actionable Results
Get clear, prioritized recommendations that your team can implement immediately.
Ongoing Support
We don't just test and leave - we provide continuous guidance and support.
Insight
Stay ahead with the latest publications, research briefs, and expert perspectives on cybersecurity.
Web App Penetration Testing
Driving Portfolio-wide Value with Cybersecurity
Atumcell Publications
Explore our latest whitepapers, case studies, and reports designed to strengthen security strategy.
Frequently Asked Questions
Web applications are often the most exposed part of your business and a common entry point for attackers. Customer portals, internal platforms, APIs, and admin panels can contain vulnerabilities that lead to data breaches, account compromise, financial loss, or operational disruption. Penetration testing helps identify these weaknesses before attackers do, reducing risk, supporting compliance requirements, and protecting both your business and customer trust.
We follow OWASP Testing Guide v4, PTES, and WSTG. Testing covers the OWASP Top 10, business logic flaws, authentication and authorization weaknesses, API security, and custom application-specific attack vectors.
Yes. We test both anonymous and authenticated user flows, including privilege escalation paths and lateral movement between user roles.
Yes. REST, GraphQL, and SOAP APIs are in scope. We test for injection, broken object-level authorization (BOLA/IDOR), mass assignment, and rate-limiting bypass vulnerabilities.
We can typically begin within 5 business days of scoping sign-off. Contact us to check current availability.
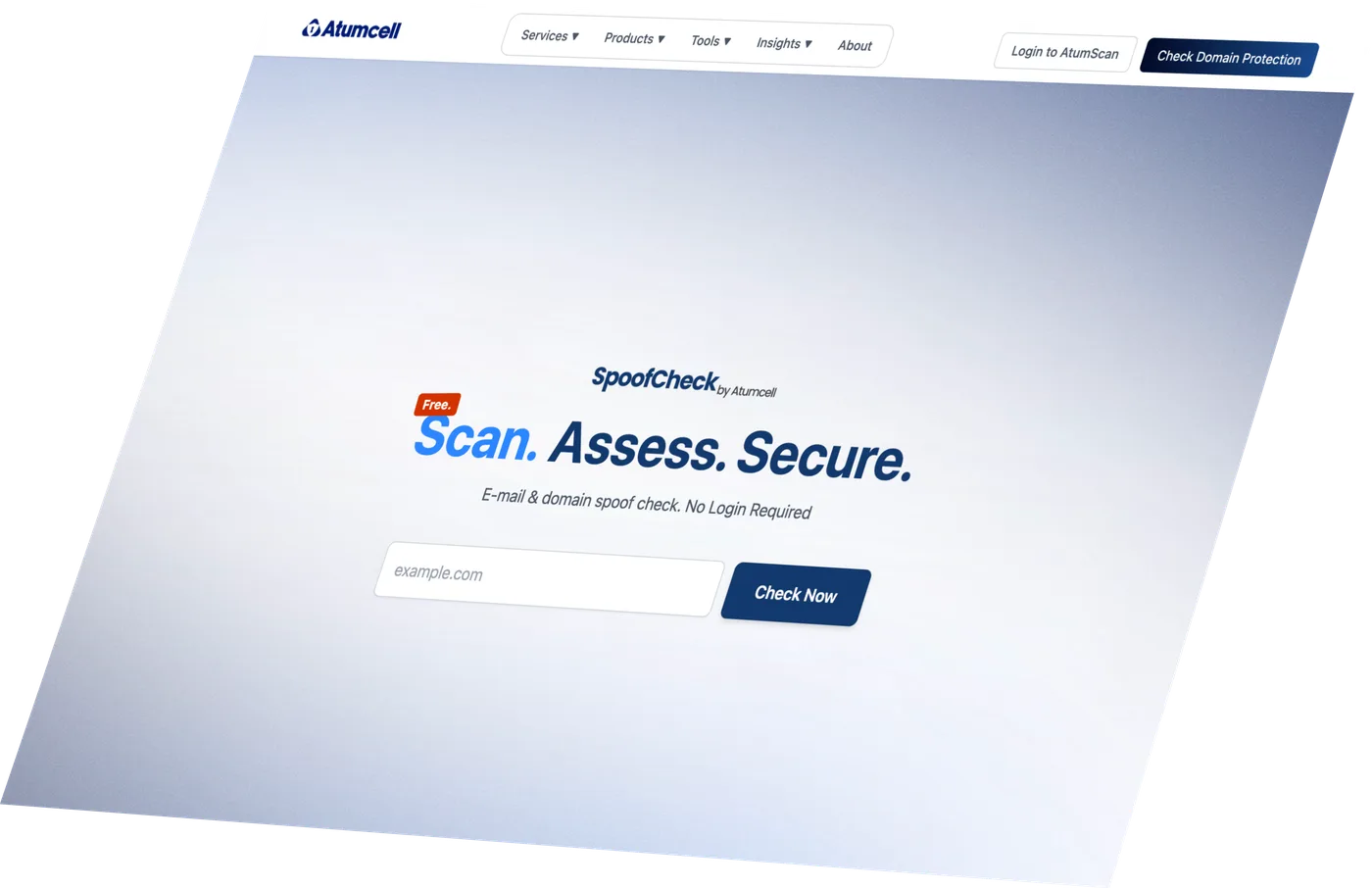
Discover Your
Cyber Risk Level.
Find out in seconds if your domain can be spoofed. Free, no login required.
Fixed-scope pricing agreed before we start · Actionable insights · No commitment required